Microsoft has released patches to fix numerous vulnerabilities in the February 2023 Patch Tuesday release including remote code execution in Exchange Server.
Official announcement can be found here.
Microsoft has released Security Updates (SUs) for vulnerabilities found in:
- Exchange Server 2013
- Exchange Server 2016
- Exchange Server 2019
To learn more about these vulnerabilities, see the following Common Vulnerabilities and Exposures (CVE):
- CVE-2023-21529 – Microsoft Exchange Server Remote Code Execution Vulnerability
- CVE-2023-21706 – Microsoft Exchange Server Remote Code Execution Vulnerability
- CVE-2023-21707 – Microsoft Exchange Server Remote Code Execution Vulnerability
- CVE-2023-21710 – Microsoft Exchange Server Remote Code Execution Vulnerability
Issues that are fixed in this update:
Export-UMPrompt fails with InvalidResponseException
Edge Transport service returns an “EseNtOutOfSessions” Exception
Some Exchange services do not start automatically after installing January 2023 Security Update
Data source returns incorrect checkpoint depth
Serialization fails while tried accessing Mailbox Searches in ECP
Transport delivery service mishandles iCAL events
SUs are available for the following specific versions of Exchange Server:
- Exchange Server 2013 CU23 (note that support and availability of SUs end on April 11, 2023)
- Exchange Server 2016 CU23
- Exchange Server 2019 CU11 and CU12
The February 2023 SUs address vulnerabilities responsibly reported to Microsoft by security partners and found through Microsoft’s internal processes. Although we are not aware of any active exploits in the wild, our recommendation is to immediately install these updates to protect your environment.
These vulnerabilities affect Exchange Server. Exchange Online customers are already protected from the vulnerabilities addressed in these SUs and do not need to take any action other than updating Exchange servers in their environment.
More details about specific CVEs can be found in the Security Update Guide (filter on Exchange Server under Product Family).
Update installation
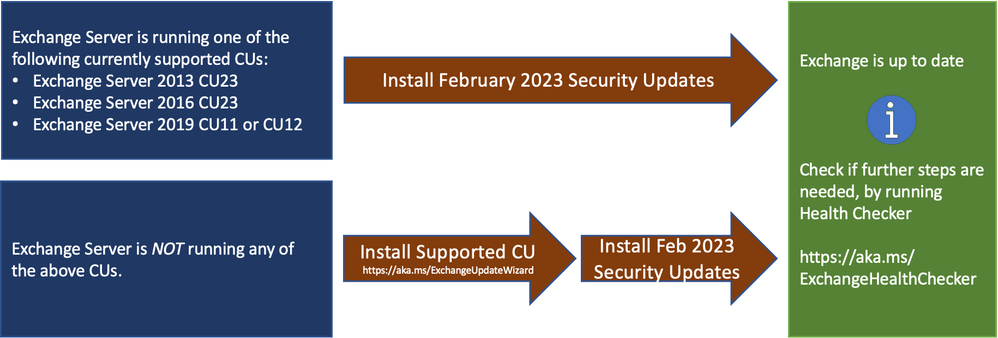
- Install the latest CU. Use the Exchange Update Wizard to choose your current CU and your target CU to get directions.
- Inventory your Exchange Servers to determine which updates are needed using the Exchange Server Health Checker script. Running this script will tell you if any of your Exchange Servers are behind on updates (CUs, SUs, or manual actions).
- Re-run the Health Checker after you install an SU to see if any further actions are needed.
- If you encounter errors during or after installation of Exchange Server, run the SetupAssist script. If something does not work properly after updates, see Repair failed installations of Exchange Cumulative and Security updates.
Known issues with this release
- Exchange Toolbox and Queue Viewer fails after Certificate Signing of PowerShell Serialization Payloa… (Note: this is an issue with the Certificate Signing of PowerShell Serialization Payload feature, not an issue with the security update)
Issues resolved in this release
- Version error when you install Exchange Server in RecoverServer mode – going forward, February 2023 and newer SUs will not cause this issue (but modifications made by the January 2023 SU might still require manual action during a server recovery operation, so the steps outlined in the article might still apply with later SUs installed)
- After the January 2023 SU is installed on Exchange 2016 or Exchange 2019, web page previews for URLs shared in OWA do not render properly
- Some Exchange services do not start automatically after installing January 2023 Security Update
- PowerShell Serialization Payload Signing can now be enabled if Exchange Server 2013 is in the organization
Reach out to Messageware to improve Microsoft Exchange Server Security
If you are not protecting all the protocols used by your Exchange Server, you’re putting your company at a higher risk of a data breach.
Security incidents happen frequently. They cause disruption, loss of data and potentially risk the reputation of your company. However, if you implement these steps, you’re doing more than most other companies.
Have you heard about Messageware’s EPG that offers advanced Exchange Server security to protect organizations from a variety of logon and password attacks, as well as extensive real-time reporting and alerts of suspicious logon activity? Click here to learn more.
